Security at Truto: How Truto Helps You and Your Customer Rest Easy
Safeguarding data isn't just a line item—it's a complex, critical task. Deep dive into the practices we follow at Truto to keep your data secure.
When you build native integrations with third-party platforms, safeguarding data is a hard engineering requirement. The challenge multiplies with the variety of attack vectors that come into play. At Truto, we treat data security as a core primitive. In this post, we'll walk you through the multilayered security measures we've implemented to ensure the privacy and security of your customers' data.
Truto does not store your customer's data
Truto operates as a pass-through proxy for your integration payloads. We do not retain your customers' data. All data is fetched and transmitted in real time without being stored on our servers or cached in our databases. This stateless approach ensures you receive just-in-time information directly from the source API, eliminating the risk of stale data. More importantly, it removes Truto as a vector for data breaches - if we don't store the payload, it can't be exfiltrated from our systems.
Limit scope
We enforce the principle of least privilege. With Truto, you and your customers define the exact OAuth scopes required for the integration to function. We only request the permissions necessary to execute the specific API calls you configure, preventing over-privileged access to third-party accounts.
Tailored Permissions
Beyond standard OAuth scopes, RapidForm - our drop-in authentication UI - lets your customers grant resource-level access. Instead of authorizing an entire workspace, a customer can restrict access to specific files, folders, or databases. For instance, a user connecting Notion can select individual pages to share, keeping the rest of their workspace completely isolated.
Business Verification
Phishing and OAuth consent spoofing are real threats. We rigorously vet every business on our platform to prevent business identity theft. This verification process protects end-users from inadvertently connecting their third-party applications to malicious or unauthorized entities impersonating legitimate software. Learn more.
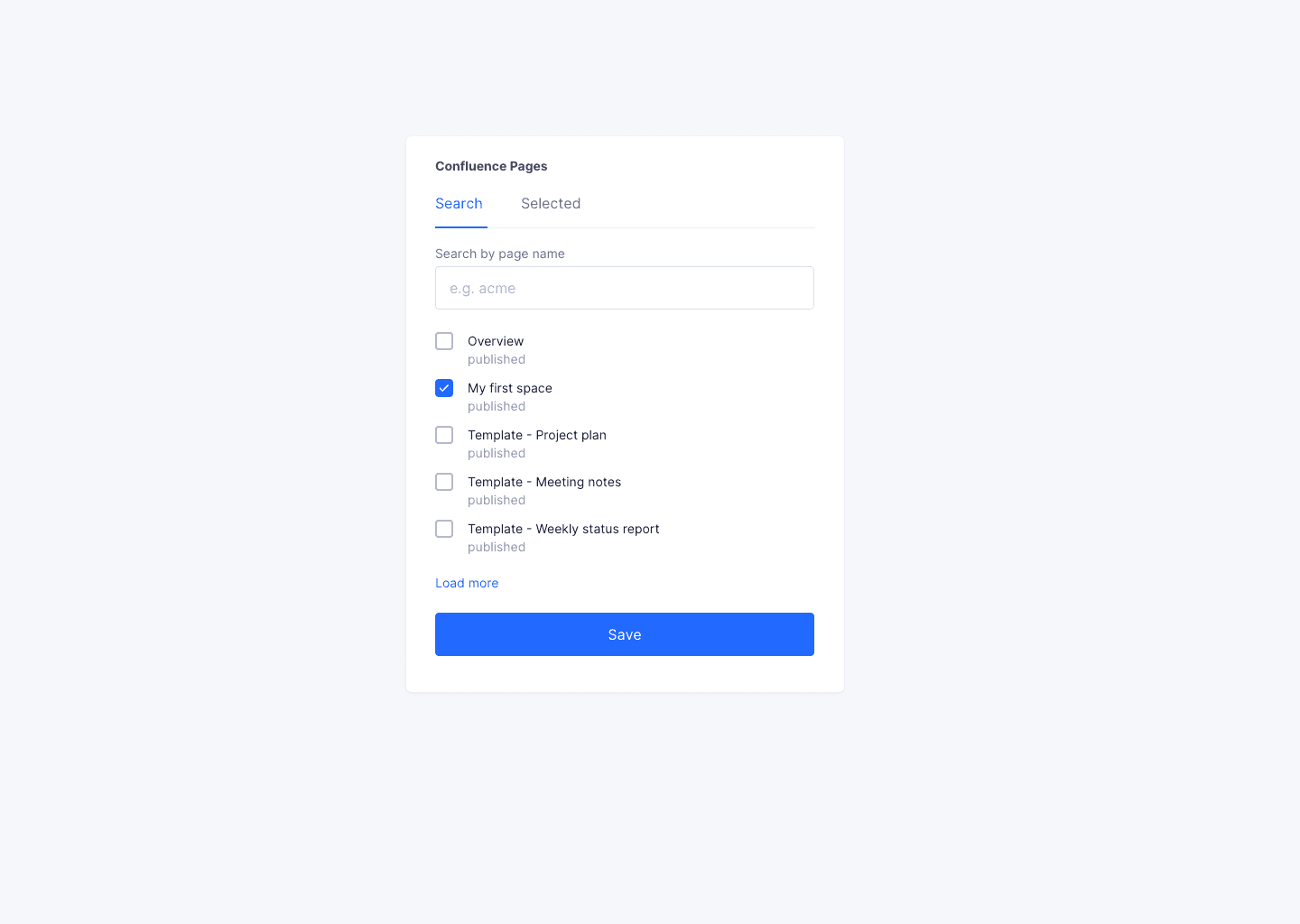
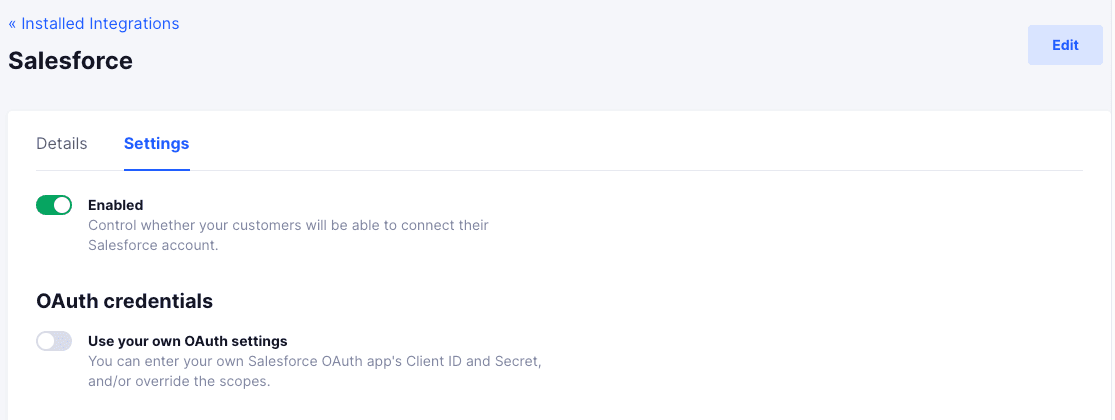
Add your OAuth credentials
While Truto provides a shared OAuth app for rapid prototyping, production environments demand isolation. You can input your own OAuth client IDs and secrets. Once configured, Truto routes all authentication through your dedicated app. This white-labels the consent screen for your users, isolates your API rate limits from other Truto tenants, and ensures you retain full ownership of the app review process.
Regional Token Storage
Data residency requirements like GDPR and CCPA often dictate where infrastructure must live. Truto gives you the flexibility to store access tokens, API keys, team member data, and basic connection metadata in a geographic region of your choice, ensuring compliance with local data protection laws. Learn more here.
Self-hosting/On-premise Deployment
For organizations with strict compliance or air-gapped requirements, Truto offers a VPC (Virtual Private Cloud) deployment model. You can host the Truto data plane directly within your own AWS, GCP, or Azure environment. This guarantees that API requests, access tokens, and integration traffic never leave your network perimeter. This feature is available on our Enterprise plans. See all pricing plans.
Encryption at Rest and in Transit
All stored credentials - including OAuth refresh tokens and API keys - are encrypted at rest using AES-256. In transit, all API traffic between your application, Truto, and the third-party providers is secured using TLS 1.2 or higher, preventing man-in-the-middle attacks.
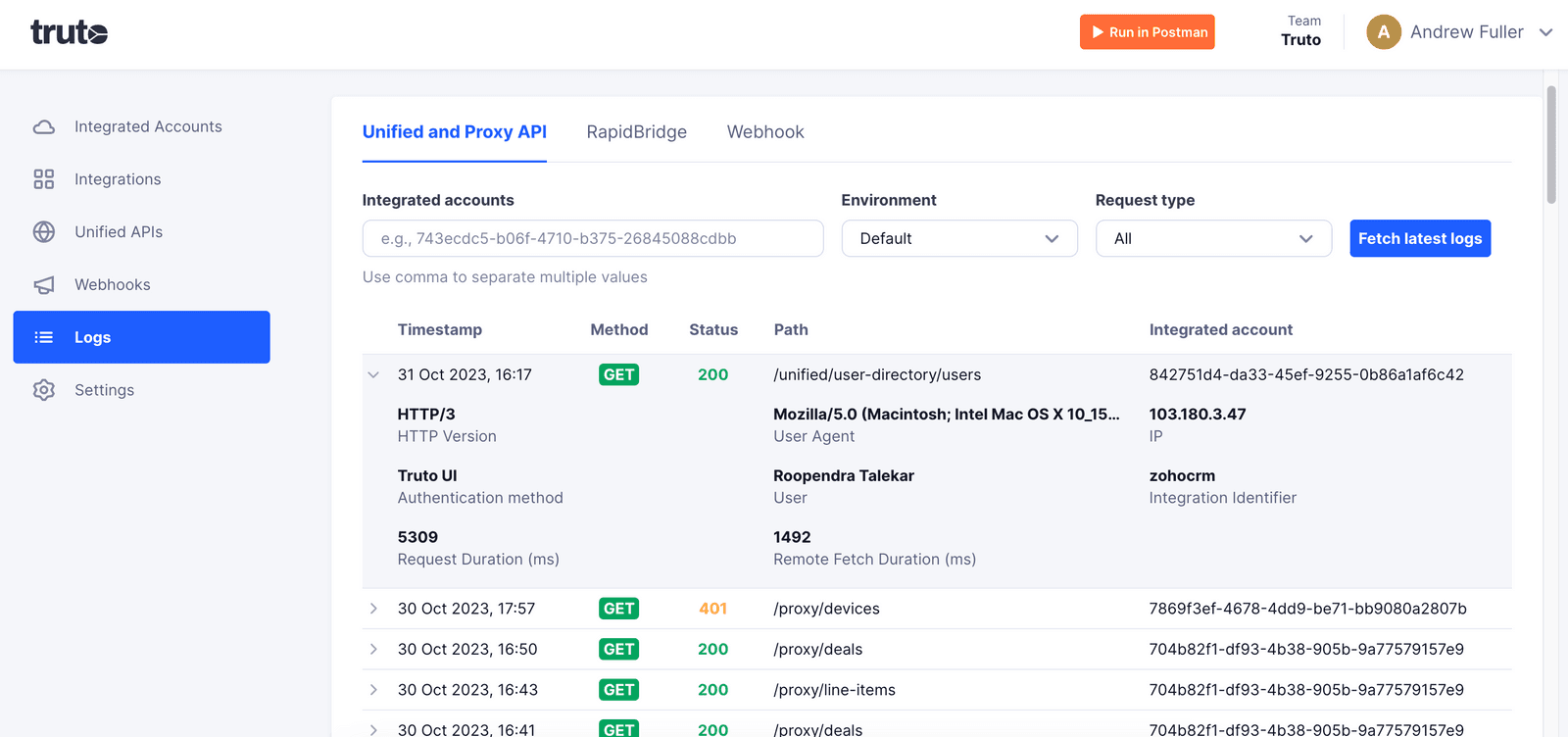
API Logs
Observability is a baseline requirement for debugging integrations. Truto offers detailed logging of all API requests, including headers, status codes, and latency metrics, with a retention period of up to 180 days. To maintain our zero-data-storage guarantee, sensitive payloads and authorization headers are automatically masked or stripped before logs are written.
Compliance
We undergo regular independent audits to validate our security posture. Truto maintains SOC 2 Type 2 compliance, ensuring our internal controls for security, availability, and confidentiality are continuously monitored. We also provide HIPAA-compliant infrastructure and execute Business Associate Agreements (BAAs) for healthcare customers, while fully adhering to GDPR requirements for data privacy.
To sum it up, your peace of mind is our priority. We don't just offer tools for building integrations; we've engineered our platform with security as a default state. From resource-level permissions to AES-256 encryption, and from zero data storage to strict compliance standards, Truto is designed to be a secure foundation for your infrastructure.
Thank you for entrusting us with your integration needs. Feel free to reach out to us at support@truto.one with any questions or for more information.
FAQ
- Does Truto store my customer's data?
- No, Truto does not retain your customers' data. All data is fetched and transmitted in real time without being stored on Truto's servers to reduce the risk of data breaches.
- What encryption standards does Truto use for tokens?
- Truto safeguards all stored access tokens and API keys using AES-256 encryption standards.
- Is Truto SOC 2 compliant?
- Yes, Truto meets SOC 2 Type 2 and HIPAA compliance standards and is also GDPR certified.
- Can I deploy Truto within my own cloud environment?
- Yes, Truto allows for self-hosting and on-premise deployment within your own Virtual Private Cloud (VPC) to ensure data never leaves your secure environment.